Traditional security methods are failing against modern threats.
What traditional code
scanners give you
scanners give you
Hundreds or thousands of unprioritized possible issues
30-70% of issues identified end up as either false positives or inconsequential findings
What Xint Code gives you
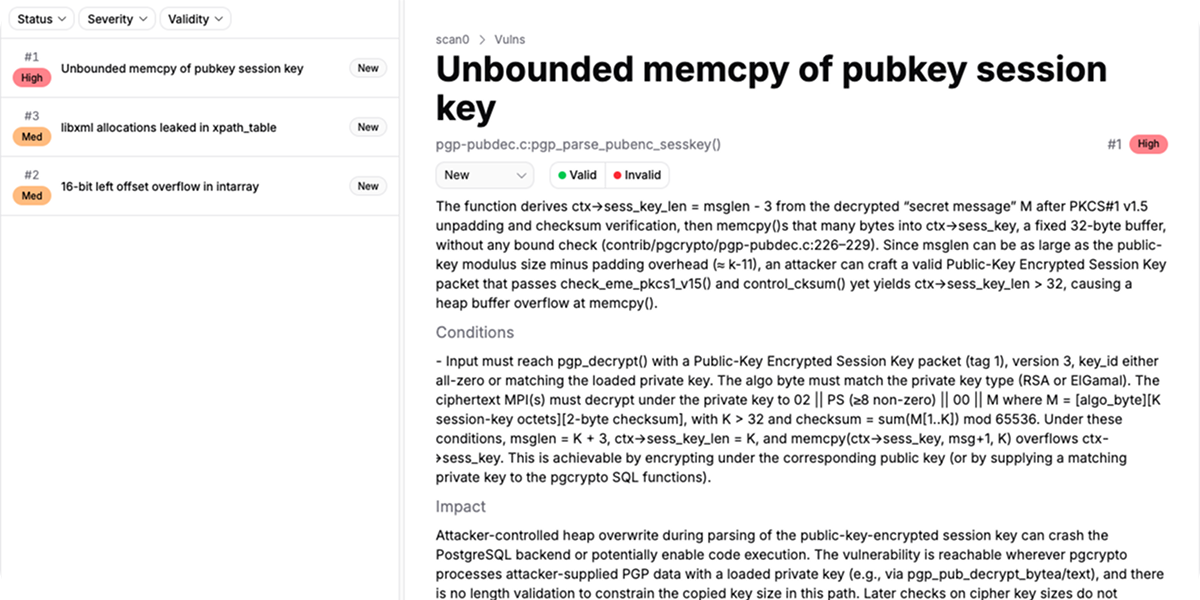
Prioritized list of findings
What steps does a hacker need to take in order to trigger the vulnerability
What does the attacker get after exploiting the vulnerability
How Xint Code Works
Connect your repo
No code packaging or harnessing required

Watch it work
Thousands of parallel AI agents search for security issues
Fix your project
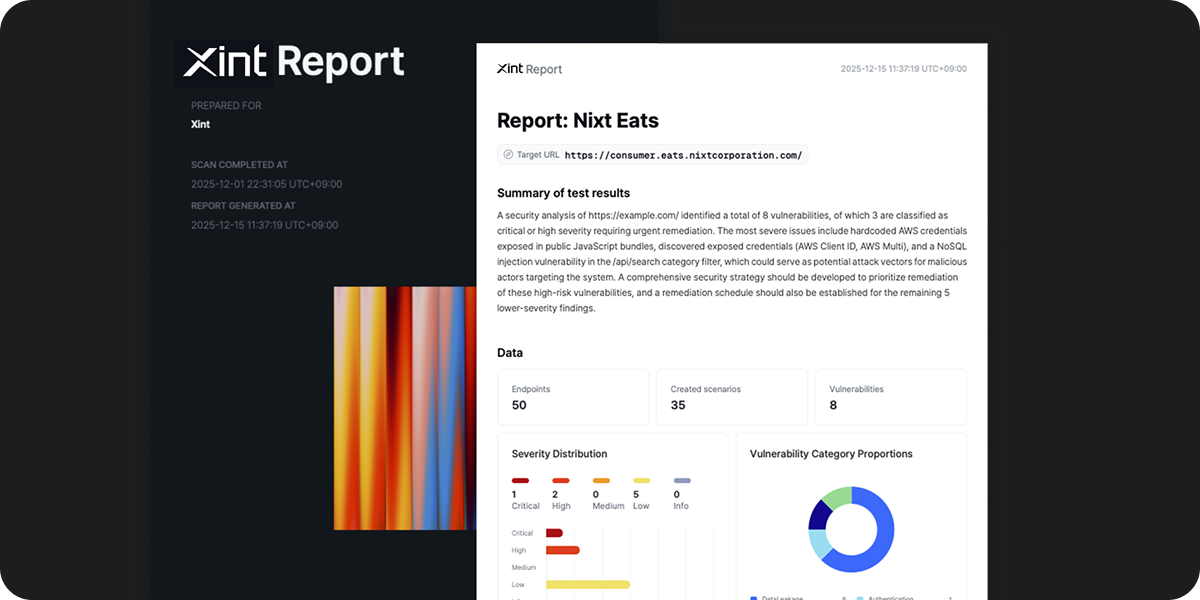
Output is human readable reports prioritized by severity, with trigger/impact narratives
Legacy scanners drown AppSec teams in false signals. Xint wins head-to-head by focusing on high impact vulnerabilities that others missed.
Our team of leading offensive security researchers have won several of the most prestigious global security challenges with Xint technology.
With zero human intervention, Xint found critical 0day RCE bugs in Redis, PostgreSQL, and MariaDB – sweeping the database category at ZeroDay Cloud, beating out every human team.

Top-3 in the AI Cyber Challenge hosted by DoD DARPA
9x DEF CON winner, the global record for the largest hacking competition in the world.

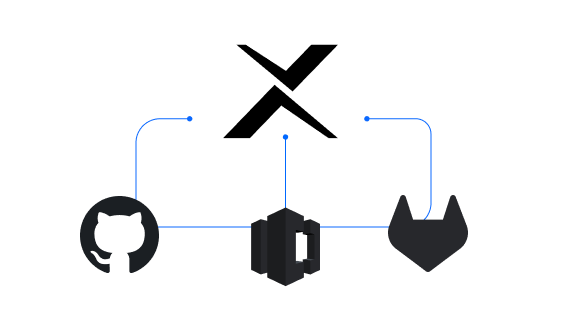
Just upload your file
Other solutions require you to package your code before analysis. Xint requires no formatting, packaging, or harnessing. Simply upload your repo and start the scan.